|
So 2FA – or its cousin, Multi-Factor Authentication (MFA) – is a better way to secure things, as a remote system can validate that the user knows something which identifies them (their username & password, secret phrase, date of birth etc etc) but also has something that identifies them too; a security token, smart card, digital certificate or something else that has been issued, or even just a mobile phone that has been registered previously with whatever is trying to validate them. Although such systems have been around for a while, the average punter in the EU has been more recently exposed to 2FA through a banking directive that requires it for many services that involve transfer of funds, setting up payments or even using credit cards. In some cases, the tech is pretty straightforward – you get a SMS text message with a 6-digit one-time code that you need to enter into the mobile app or website, thus proving you know something (you’re logged in) and you have something (your phone), so validating that it really is you. Or someone has stolen your phone and your credentials… MFA is stronger than 2FA, as you can combine what you know and what you have, with what you are. An example could be installing a mobile banking app on your phone then enrolling your account number, username & password; the know is your credentials, and the have is a certificate or unique identifier associated with your phone, as it’s registered as a trusted device by the banking service that’s being accessed. Using your fingerprint to unlock the app would add a 3rd level of authentication – so the only likely way that your access to the service (for transferring funds or whatever) could be nefarious, is if you are physically being coerced into doing it. 2FA and MFA aren’t perfect but they’re a lot better than username & password alone, and Microsoft’s @Alex Weinert this week wrote that it’s time to give up on simpler 2FA like SMS and phone-call based validations, in favour of a stronger MFA approach. And what better way that to use the free Microsoft Authenticator app? Once you have Authenticator set up and running, It’s really easy to add many
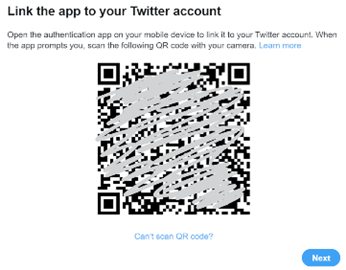
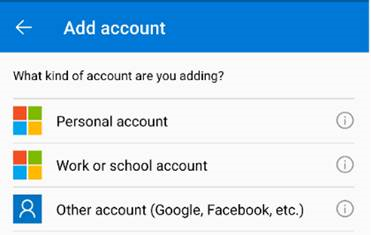
In the Microsoft Authenticator app itself, add an account from the menu in the top right and then choose the option that it’s for “other” – presuming you’ve already have enrolled your Work or school Account (Microsoft/Office 365) and your Personal account (MSA, ie Outlook.com etc). After tapping the option to add, point your phone at the QR code on the screen and you’re pretty much done; you’ll need to enter a one-time code to confirm it’s all set up – rather than getting an SMS, go into the list of accounts in the Authenticator app home screen, open the account you’ve just added then enter the 6-digit code that’s being displayed. This is the method you’ll use in future, rather than waiting to be sent the 6-digit code by text. As you can see from the description, there are lots of other 3rd party apps and websites that support MFA using authenticator apps –
|