|
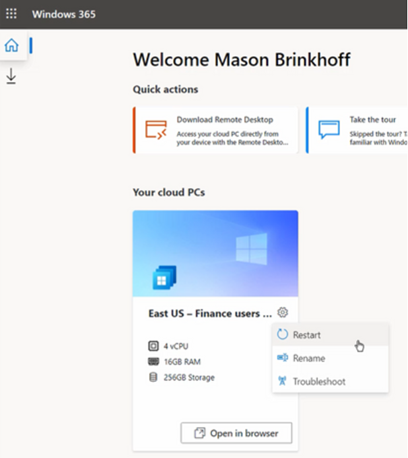
Windows 365 delivers a “Cloud PC” – literally a machine running Windows, which is remotely accessed by an end user and stays just like they left it when they disconnect, but is managed and secured centrally. As you may expect, there will be various SKUs depending on how capable you want it to be; Paul Thurrott opines that there will be many options, as “Microsoft is addicted to tiers”. General Availability is due on 2nd August; it’s sits on top of the existing
According to Mary Jo Foley, it will be reassuringly expensive so use cases will be carefully chosen rather than thinking everyone will sit at home running W365, accessing it over some ancient PC. For more details on machine sizing and the mechanics of provisioning and managing Windows 365, see here. Interesting examples given during the announcement were the remote government of Nunavut, or having hundreds of interns joining Microsoft for the summer; normally they’d come to the office and be given a PC but since they’re all at home, the cost and time burden of configuring the PCs and shipping them out would have been high. Instead, they’re given a virtual desktop via Windows 365 – created en masse in a few minutes – and they connect to that from whatever kind of device they already have at home. When their tenure is up, their access is removed and there’s no data left behind on their iPad/Mac/Chromebook or home PC. Maybe 2022 could finally be the Year of the Linux Desktop? For the rest of us; Windows 10 is still moving forward and the latest release due later this year has entered its latest stage of testing – Windows 10 21H2. And Windows 11 got another update to 22000.71, offering a variety of tweaks and polish. Even though Windows 10 is a modern OS with lots of great functionality, if you have already switched to Windows 11, using a machine with Win10 feels like going back in a time machine. |
Tag: Azure
586 – Pick Up Thy WordPress
|
The extended back story is that there were hundreds of employee blogs which had been published under the technet.microsoft.com and msdn.microsoft.com sites, both of which URLs could trace their birth back to the 1990s, and a project was underway to clean them up and rationalize somewhat. Initially, guidance to MS bloggers was (basically) “unless you’re an official blog, you have <nn months> to move your stuff elsewhere before it gets deleted.” Certainly, there was to be no new content after the cut-off date.
That guidance relented somewhat and content from relatively active blogs was migrated to the Microsoft Docs archive though taking a trip through the final posts from the ToW host blog, The Electric Wand, shows that lots of graphical content was not carried across – more of a lift & dump than a lift & shift. Blogging is a bit old-hat these days but lots of people do still maintain a blog to share stuff they think is interesting; see Scott Hanselman as one example. Anyway, the solution for Tip o’ the Week was to move to an external website – www.tipoweek.com – which is hosted in Azure and, like about a third of all websites, running under the content management system, WordPress.
For more tips on how best to get up and running with WP in Azure, see here.
This has, in fact, been a niggling issue for a while, since Chrome (and Edge, given its diet of Chromium) instituted a policy of flagging any website that doesn’t use the secure HTTPS protocol & SSL by default. Secure Sockets Layer, if you’re not overly familiar with it, relies on a way of encrypting data travelling between two points, using a previously-generated pair of mathematically-linked digital keys. If you have one key, you can use it to encrypt data which can only be decrypted by the other key in the pair (ie you can’t even use the same key that encrypted the data to decrypt it again). Typically, one of these keys is publicly accessible and the other is kept private.
The whole public/private key encryption process has something of a computational overhead associated with it, but once we have established a secure connection, we could use a faster encryption technique for data sharing by using a single key that can both encrypt and decrypt the same data. In other words, if I go to a website that presents me a certificate specifically issued for that URL’s domain, I can be sure that the site handing out the cert is who they purport to be. This could be validated by me generating a random set of numbers, encrypting it with the public key and sending that to the site; it would decrypt the gobbledygook with the private key that only it has, and we now both have the same set of data that has been securely shared between us. That would form the symmetric key that we can use for the rest of the connection. For more detail on these kinds of topics, check out the Cryptography 101 podcast on Hanselminutes.
The trouble is, if you’re hosting a hobby or a community web site, paying for an SSL certificate might seem a bit of overkill; web hosting companies will try to bundle them into domain protection and other security features which might be no big deal for a commercial enterprise but a little stiff for a parish newsletter. Fortunately, there are alternatives, though they do need a bit of spade work to get up and running. Hanselman (yes, him again) discussed using an extension and an organisation called Let’s Encrypt, whose goal it is to make the web 100% secure. They have issued over 225 million SSL certs, and will generate 3-month-validity certificates free of charge, as an alternative to paying anything from $60-200 a year to a commercial issuer. With a bit of practice, it doesn’t take long to create and manage the certs and if you only need to do it 4 times a year, then it could be time well spent and money well saved.
Once you have the certificate exported to a file, it’s a matter of a few clicks to import it into the Azure App Service that is running WordPress, set up the bindings appropriately, and you can then flick the switch to make the site only service up content over HTTPS.
|
Tip o’ the Week 479 – Tipping in Public
|
After some years, the Technet/MSDN blogs moved to WordPress, an open-source blog platform based on PHP and MySQL (the P & M, and mostly, on the L & A in the LAMP stack, that was once seen as antithesis of Microsoft, before Linux Love settled in).
Not all the Tip o’ the Week content moved online, mind. Some Tips were basically internal-only, or were slightly edited from the version sent in the Friday email. By and large, though, the weekly mail content went onto the blog – sometimes delayed by a few weeks. The time has come the Tip o’ the Week public blog to move – here on www.tipoweek.com. Running on WordPress, on Azure, obvs. Share widely, as you see fit. |
Tip o’ the Week 430 – developers, developers, developers
|
Apple has its WWDC in California every year (for a long time, in San Francisco), and at its peak was a quasi-religious experience for the faithful. Other similar keynotes sometimes caused deep soul searching and gnashing of teeth. The Microsoft one used to be the PDC, until the upcoming launch of Windows 8 meant it was time to try to win the hearts & minds of app developers, so //build/ became rooted in California in the hope that the groovy kids would build their apps on Windows and Windows Phone. Now that ship has largely sailed, it’s gone back up to the Pacific North West, with the focus more on other areas.
With Azure Sphere, there’s a way for developers to build secure and highly functional ways to process data on-board and communicate with devices, so they can concentrate more on what their apps do, and on the data, less on managing the “things” which generate it. For all of the breakouts at Build and the keynotes on-demand, see here. Back in the non-cloud city, Google has adopted a similar developer ra-ra method, with its Google I/O conference also taking place in and around San Francisco, also (like WWDC and Build) formerly at Moscone. It happened this past week, too. Like everyone else, some major announcements and some knock-em dead demos are reserved for the attendees to get buzzed on, generating plenty of external coverage and crafting an image around how innovative and forward thinking the company is. Google Duplex, shown this week to gasps from the crowd, looks like a great way of avoiding dealing with ordinary people any more, a point picked up by one writer who called it “selfish”. Does a reliance on barking orders at robot assistants and the increasing sophistication of AI in bots and so on, mean the beginning of the end for politeness and to the service industry? A topic for further consideration, surely. |
Tip o’ the Week 419 – What’s the time?
|
Windows 10 tweaked the way time is In the Windows Insiders builds of the last few weeks – currently 17101 (which is now in the Fast Ring), there have been changes that bring the clock further forward too – the Game Bar has been updated to include the clock on the What is time? Existentially, time is relative. If you ever find that your Windows PC isn’t keeping time accurately, you may want to check that you have it set to get its time automatically (check Settings -> Time & Language – > Date & time), or go into the old-fashioned Control Panel, search for time and look at the settings in there, especially under the “Internet Time” tab to see where it’s syncing the time from: time.windows.com is probably the default. Windows Time is also a thing – the number of milliseconds since the machine was started up, and also the name of the Back to simple relativity, though – what is the actual, real “time”? If you have multiple clocks, watches, phones & PCs, it’s a fair bet that they’ll all be divergent, unless they’re all being synchronised by some external device (your broadband router, maybe). If you’d like to find out exactly what the time is and don’t have access to an atomic clock or similar, there are a few online resources that might help… and you could even try asking Cortana, as she knows about time zones and stuff. But the best time site is http://time.is. Try it from any device and you’ll get the time right now; some allowances need to be made for network latency but the operators have tried For an illustration of what latency (as ultimately governed by the speed of light) means when accessing nearby vs far away websites, check out www.azurespeed.com, which measures the time to connect to storage services at Azure datacenters. Some variance could be explained by performance spikes and so on, but the main impact is network latency due to distance travelled. The results can sometimes be surprising. |
Tip o’ the Week 354 – Alone in the Dark
|
There’s a school of thought that it’s easier to read light coloured text on dark backgrounds than the other way around, even though we’re conditioned to have black text on white paper. It’s largely a personal preference thing, so might be worth having a play with a few options within Office & Windows (and a few other apps) to see how you fare.
Go into Settings -> Personalization -> Colors to tweak the app mode on your PC. The Edge browser inexplicably ignores the app mode on the main settings page, but does implement its own light/dark theme, accessed via the Settings (click or tap the … in the top right, then Settings).
Users of Visual Studio and the Azure Portal probably know this already but they also feature dark themes… |
Tip o’ the Week 328 – Clip for art’s sake
|
If you’re after some high-quality clip art to insert into you magnus opus, you could try a service called Pickit, previously known as PicHit.me. The Pickit Photo Finder app gives you a nice Modern app way of finding cool photos given a theme or keyword (though there’s a subscription fee if you want the higher quality pics). It’s even Cortana enabled, supposedly. There’s an Office Addin too, which lets you search for and add photos and art straight into your documents. Pickit is a Microsoft BizSpark success story, and the service runs on Azure. There are many ways of finding decent clipart for your projects – there’s Open Clip Art for an archive of more traditional vector & standard clipart image fare, or image hosting services like Pixabay, which offer free Creative Commons photos. Check out these other alternatives too. |
Tip o’ the Week #192 – What does your customer run?
If you are in the tech industry and dealing with a customer or partner on pretty much any aspect of their relationship with you, it can often be valuable to have a bit of forewarning about what technology they’re using. In larger managed environments, that knowledge might come from other resources (account manager, technical pre-sales, support contact etc), it may be tucked away in your email from an old thread.
Who knows, it might even be in CRM.
Even if you’re working with a well-engaged entity, it can still be helpful to do a little background research, and that’s near-mandatory if the org in question is new to us all. Here are some thoughts on how to get ahead of the game without needing to spend hours at the task.
This is now an essential business tool for a lot of people, as it both projects their CV into the world so a potential next employer can see it, and it helps them connect with people in other organisations they’re trying to reach. Before you meet your customer, it’s worth looking up the company and seeing who else works there, what skills the individuals have (eg do they position themselves as an Open Source or Linux expert? Are they certified to the hilt in your stuff already, and therefore maybe a friendly face?). Who did they work for previously?
One tip for the practiced LinkedIn stalker is that it’s possible to switch off the breadcrumbs that let people see who’s looked at their profile, so if you check someone out and decide to have nothing more to do with them, you won’t end up getting a connection request in return as they’ll never know it was you.
Go to the Privacy & Settings option by clicking your mugshot in the  top right then Select what others see when you’ve viewed their profile, whereupon you can choose full disclosure, partial anonymity (so they’ll see it was someone at Microsoft, for example – might freak them out if they are LAMP fiends) or the full kahuna of diplomatic immunity.
top right then Select what others see when you’ve viewed their profile, whereupon you can choose full disclosure, partial anonymity (so they’ll see it was someone at Microsoft, for example – might freak them out if they are LAMP fiends) or the full kahuna of diplomatic immunity.
You might also want to think about who gets to see your connections – if you get lots of requests from people you don’t know, they may just be trying to harvest your own connections (as they’d see more details of those users, since they’d now be 2nd degree connections to the recruitment consultant connection spammer). We’ll come back to using LinkedIn in a future ToW.
Mxtoolbox – www.mxtoolbox.com
This one is useful for checking what your customer is using for their email, or at least which service they’re using to clean and filter their in- and out-bound email. Simply enter the customer’s email domain name (the bit after the @) and you’ll find out how they send and receive mail. Sometimes, it’ll be their own address (meaning, they operate their own relay) but often, it’ll be one of a variety of 3rd party “hygiene” services from the likes of Microsoft (Frontbridge, Outlook), Google (Postini), Symantec (MessageLabs) and more.
Netcraft – www.netcraft.com
Their “What’s that site running?” tool and web site survey made Netcraft well known years ago – ostensibly telling you what operating system the web site in question is running on. A useful side effect in these cloudy days is that it can tell you not just what the site is, but where it is running. Handy to know if your customer’s site (or maybe a subset of it which is presenting a web application to their customers?) is running on Azure, AWS, Rackspace etc. Just head over to netcraft.com and paste the URL into their “what’s that site running” box in the lower right – no need to strip it of http:// or any other superfluous guff; the site takes care of all that for you.
Is it really on Azure? – http://www.kloth.net/services/nslookup.php
Here’s a neat service which lets you check for CNAMEs of a particular URL – in other words, when you enter a URL into your browser, that name may just be an alias for another name, which you’ll never see. Knowing that such a thing exists can be handy, though – it might let you figure out that one part of the website is hosted in one place, but another part is somewhere else.
In this case, you do need to trim any leading or trainling gubbins off the URL, so you’re left with simply the main part. Sometimes the real meat of what a website is offering – the bit of the site you need to log into, for example – might be on a different URL (like login.company.com). If you plug that URL into this handy name lookup tool, and set the option to be looking for ANY or CNAME, then you may see that login.company.com is just an alias for something.cloudapp.net – the clouapp.net bit meaning that it’s a service running on Windows Azure. Not a very efficient way of looking for Azure users en masse, but if you think your customer is already on Azure, it is a handy way of confirming that fact.